This is the multi-page printable view of this section. Click here to print.
Architecture and Terms
- 1: Architecture
- 2: Terminology
- 2.1: Concepts
- 2.2: Networking
1 - Architecture
Kiali architecture
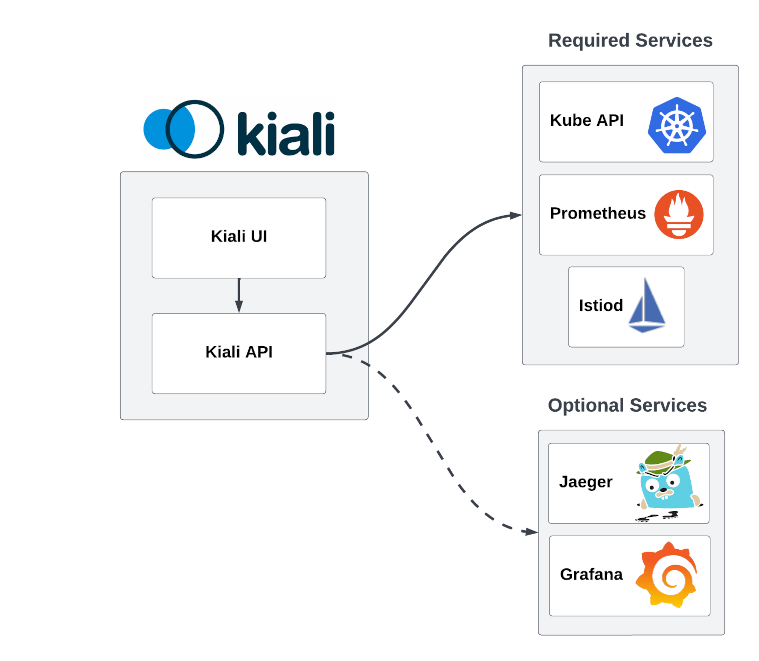
Kiali is composed of two components: a back-end application running in the container application platform, and a user-facing front-end application. Kiali depends on external services and components provided by the container application platform and Istio.
The following diagram illustrates the components involved in Kiali and its interactions:
Kiali back-end
The back-end is the application that runs in the container application platform. It’s written in Go. The code can be found at kiali/kiali GitHub repository.
This is the component that communicates with Istio parts, retrieves and processes data, and exposes this data to the front-end.
The back-end doesn’t need storage. The back-end configuration is managed via the Kiali CR when Kiali is installed via the Kiali operator, or via a configmap when installed via Helm.
Kiali front-end
The front-end is a single page web application, built using Patternfly, React, Typescript and Redux. The code can be found at kiali/kiali frontend folder.
In a standard deployment, the back-end serves the front-end. Then, the front-end queries the Kiali back-end in order to get data and present it to the user.
There are limited options for personalization, the front-end is mainly stateless. Some data may be persisted, such as session credentials, but this data is stored in the browser and won’t be available in other browsers nor other devices.
Istio Service Mesh
Kiali is a console for Istio, and as such, Istio is a requirement. It provides and controls the service mesh. Kiali and Istio are installed separately.
Kiali needs to retrieve Istio data and configurations, which are exposed through Prometheus, the Kubernetes API, and istiod. For environments where istiod is inaccessible, Kiali’s communication with istiod can be disabled.
Prometheus
Prometheus is an Istio dependency. When Istio telemetry is enabled, metrics data is stored in Prometheus. Kiali uses the data stored in Prometheus to figure out the mesh topology, show metrics, calculate health, show possible problems, etc.
Kiali communicates directly with Prometheus and assumes the metrics used by Istio Telemetery. It’s a hard dependency for Kiali, and many Kiali features will not work without it.
Currently, Kiali relies on Istio’s default metrics set. Make sure that these default metrics are always in place. Some metric customization is possible as long as the Kiali requirements are still met. For the current list of required metrics see this FAQ entry.
Kubernetes API
Kiali uses the API of the container application platform in order to fetch and resolve service mesh configurations.
Container application platforms where Kiali is known to work are OKD and Kubernetes. Kiali should also work on the derivatives of these platforms.
Kiali queries the Kubernetes API to retrieve, for example, definitions for namespaces, services, deployments, pods, and other entities. Kiali also makes queries to resolve relationships between the different cluster entities.
The Kubernetes API is also queried to retrieve Istio configurations like virtual services, destination rules, route rules, gateways, and quotas.
Jaeger
Jaeger is optional. When available, Kiali will be able to direct the user to Jaeger’s tracing data. If you need this feature, make sure Kiali is properly configured for Jaeger integration.
Tracing data will be available only if Istio’s distributed tracing is enabled.
As an alternative, Grafana Tempo can be used.
Grafana
Grafana is optional. When available, the metrics pages of Kiali will show a link to direct the user to the same metric in Grafana. If you need this feature, make sure Kiali is properly configured for Grafana integration.
Kiali has basic metric capabilities. It can show the default Istio metrics for workloads, apps and services. It allows to apply some groupings to the provided metrics and fetch metrics for different time ranges. However, Kiali doesn’t allow to customize the views nor customize the Prometheus queries. If you need these capabilities, you’ll want to install Grafana. Follow the Istio documentation to install Grafana if you need it.
2 - Terminology
2.1 - Concepts
Application
Is a logical grouping of Workloads defined by the application labels that users apply to an object. In Istio it is defined by the Label App. See Istio Label Requirements.
Application Name
It’s the name of the Application deployed in your environment. This name is provided by the Label App on the Workload.
Envoy
A proxy that Istio starts for each pod in the service mesh. For more information see the Istio Envoy Documentation.
Envoy Health
A health check performed by Envoy proxies, for inbound and outbound traffic: see membership_healthy and membership_total from Envoy documentation.
Istio object/configuration Type
This is the type specified in the Istio Config. This could be any of the following types: Gateway, Virtual Service, DestinationRule, ServiceEntry, Rule, Quota or QuotaSpecBinding.
Istio Sidecar
For more information see the Istio Sidecar definition in Istio Sidecar Documentation.
Label
It’s a user-created tag to identify a set of objects.
An empty label selector (that is, one with zero requirements) selects every object in the collection.
A null label selector (which is only possible for optional selector fields) selects no objects.
For example, Istio uses the Label App & Label Version on a Workload to specify the version and the application.
Label App
This is the ‘app’ label on an object. For more information, see Istio Label Requirements.
Label Version
This is the ‘version’ label on an object. For more information, see Istio Label Requirements.
Namespace
Namespaces are intended for use in environments with many users spread across multiple teams, or projects.
Namespaces are a way to divide cluster resources between multiple users.
Quota
A limited or fixed number or amount of resources.
ReplicaSet
Ensures that a specified number of pod replicas are running at any one time.
Service
A Service is an abstraction which defines a logical set of Pods and a policy by which to access them. A Service is determined by a Label.
Service Entry
For more information see the Service Entry definition in Istio Service Entry Documentation.
Virtual Service
For more information see the Virtual Service definition in Istio VirtualService Documentation.
Workload
For more information see the Istio Workload definition.
2.2 - Networking
Destination
For more information see the Destination definition in the Istio Glossary.
Destination Rule
For more information see the Istio Destination Rule Documentation.
Endpoint
A communication endpoint is a type of communication network node. It is an interface exposed by a communicating party or by a communication channel.
Error Rate
It’s the percentage of errors in the traffic to a specific object for a Rate Interval.
Gateway
For more information see the Gateway definition in the Istio Gateway Documentation.
Inbound Metrics
Metrics on requests received by a given Workload, Service or Application.
Outbound Metrics
Metrics on requests emitted by a given Workload or Application.
Port
For more information see the Istio Port Documentation.
Rate Interval
It’s an amount of time. By Default in Kiali last 10 minutes.
Rule
It’s an object that manages external access to the services in a cluster, typically HTTP.
Source
For more information see the Source definition in the Istio Glossary.
Subset
For more information see the Istio Subset Documentation.